Articles about Cybersecurity
Latest articles about Cybersecurity, sorted from newest to oldest.

Dji Will Pay $30k to the Man Who Accidentally Hacked 7,000 Romo Robovacs
A Chinese drone and robotics company, DJI, has made headlines after agreeing to pay a hacker $30,000 for accidentally breaching the security of 7,000 of its Romo robovacs. The incident, which occurred in 2022, highlighted the risks of IoT hacking and the importance of robust security measures in con...
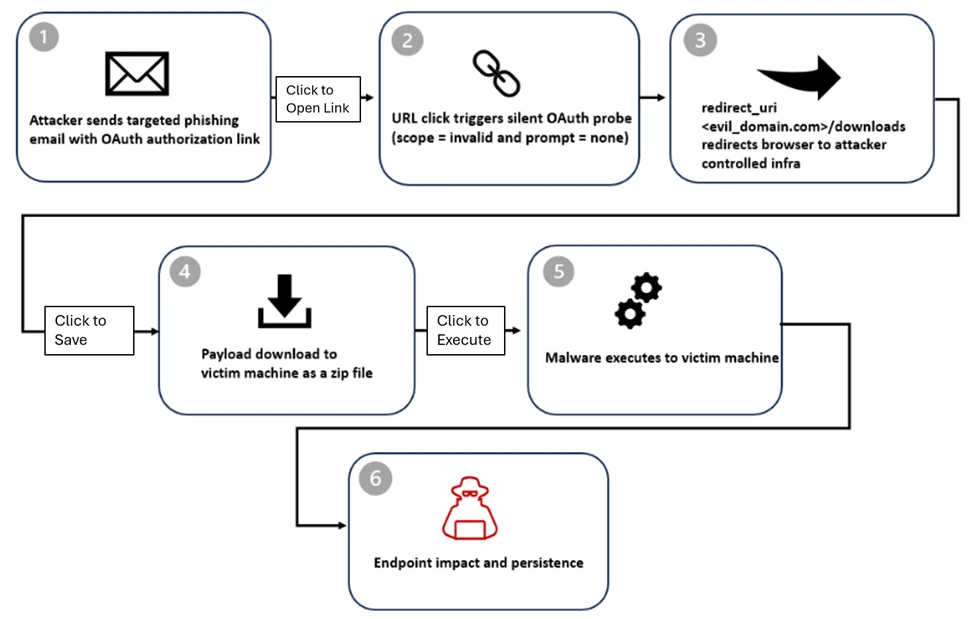
Phish of the Day: Microsoft Oauth Scams Abuse Redirects for Malware Delivery
The latest phishing scam to hit the internet involves Microsoft OAuth, a widely used authentication protocol. Attackers are exploiting this protocol to create convincing login pages that redirect users to malicious websites, where they can steal sensitive information or install malware. How the Scam...

New Airsnitch Attack Exposes Wi-fi Encryption Vulnerability
The security landscape continues to evolve with the emergence of new threats and vulnerabilities. The latest development in this area is the discovery of a novel attack that exploits weaknesses in Wi-Fi encryption, leaving millions of devices and networks at risk of unauthorized access. Exploitation...

Microsoft Error Sees Confidential Emails Exposed to Ai Tool Copilot
A recent error in Microsoft's system has exposed confidential emails to the AI tool Copilot, raising serious concerns about data security and the potential risks of using AI-powered tools. The incident has sparked an investigation into the full extent of the breach and the measures taken by Microsof...

A Mystery Phone, Found in the Desert, Slowly Reveals Its Secrets
Researchers at the University of California, Los Angeles (UCLA), made the breakthrough discovery when they were able to crack the phone's encrypted password using advanced algorithms. Initial Findings The phone was found to contain a vast amount of data, including emails, texts, and phone calls, whi...
Cisa Flags Four Security Flaws Under Active Exploitation in Latest Kev Update
The Cybersecurity and Infrastructure Security Agency (CISA) has released its latest Known Exploited Vulnerabilities (KEV) catalog update, identifying four security flaws currently under active exploitation by hackers. This update serves as a critical reminder for organizations to prioritize patching...

Microsoft Says Hackers Are Exploiting Critical Zero-day Bugs to Target Windows and Office Users
The tech giant Microsoft has issued a warning about widespread exploitation of critical zero-day bugs in its Windows and Office software. The company has confirmed that hackers are using these bugs to gain unauthorized access to user systems, compromising sensitive data and potentially leading to fu...

An Ai Toy Exposed 50,000 Logs of Its Chats with Kids to Anyone with a Gmail Account
The chat logs, which include personal conversations between the AI toy and kids, were made publicly accessible due to a security flaw in the toy's design. The logs contain sensitive information such as names, ages, and personal interests of the children who interacted with the toy. Security Flaw Exp...

Cisa Warns of Active Exploitation of Enterprise Software Bugs
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning about the active exploitation of four enterprise software bugs. These vulnerabilities affect various software applications and pose a significant risk to organizations that have not patched their systems. According to B...