The latest phishing scam to hit the internet involves Microsoft OAuth, a widely used authentication protocol. Attackers are exploiting this protocol to create convincing login pages that redirect users to malicious websites, where they can steal sensitive information or install malware.
How the Scam Works
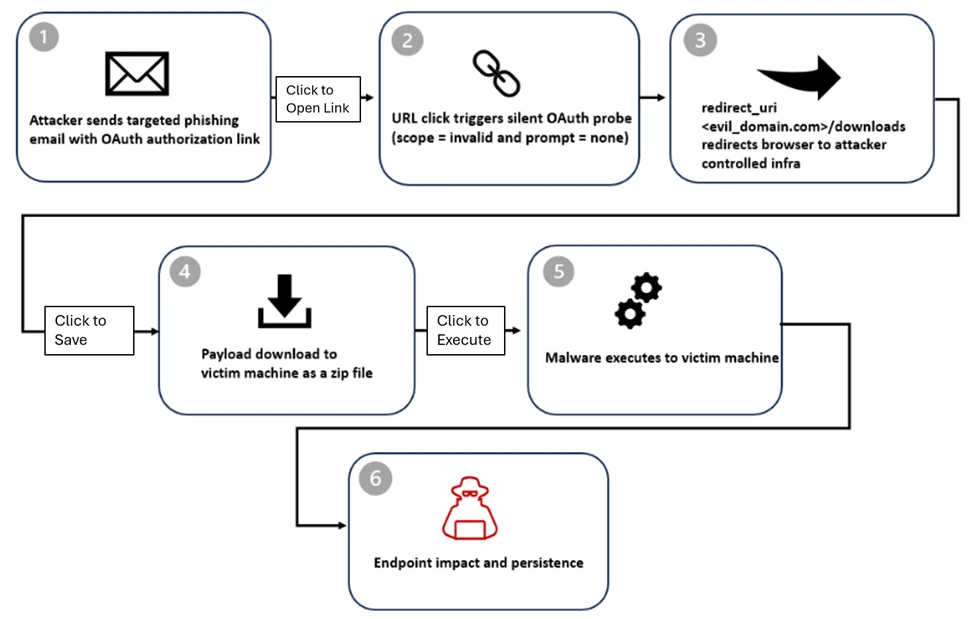
Here's how the scam typically works: an attacker creates a convincing login page that looks like a legitimate Microsoft OAuth login page. When a user enters their credentials, the page redirects them to a malicious website, where the attacker can steal sensitive information or install malware. This is often done using a technique called "spoofing," where the attacker creates a fake website that looks like the real thing.
The scam is often made more convincing by the use of legitimate-looking logos and branding. Attackers may also use social engineering tactics to trick users into clicking on links or entering credentials. For example, they may send a phishing email that appears to come from a legitimate source, such as Microsoft or a popular online service.
Risks to Users
The risks to users are significant. If a user falls victim to this scam, they may inadvertently install malware on their device, which can lead to a range of problems, including data theft, identity theft, and system crashes. In addition, users may also be exposed to other types of online threats, such as ransomware or phishing attacks.
Users are advised to be cautious when clicking on links or entering credentials online. They should always verify the authenticity of a website before entering sensitive information, and should be wary of links or emails that appear suspicious. They should also keep their software and operating system up to date, as this can help to prevent malware attacks.
Prevention is Key
Prevention is key when it comes to avoiding these types of scams. Users should always be cautious when clicking on links or entering credentials online, and should be wary of links or emails that appear suspicious. They should also keep their software and operating system up to date, as this can help to prevent malware attacks.
In addition, users can take steps to protect themselves from these types of scams. For example, they can use two-factor authentication, which requires users to provide a second form of verification in addition to their username and password. They can also use anti-virus software and a firewall to protect their device from malware attacks.
Microsoft has also announced that it will be taking steps to prevent these types of scams. The company will be implementing additional security measures to prevent attackers from exploiting the OAuth protocol, and will be working with users to educate them about the risks and how to prevent them.
In conclusion, the Microsoft OAuth scam is a significant threat to users, and requires immediate attention. Users should be cautious when clicking on links or entering credentials online, and should take steps to protect themselves from these types of scams. By being vigilant and taking preventative measures, users can reduce the risk of falling victim to these types of scams.